
It’s a CRE bling thing.
What’s better than continuously being recognized for outstanding CRE branding and marketing? Not much, really.
read moreThe year 2016 saw a crucial tipping point in the brave new world of ubiquitous computing. The sheer number of technological opportunities and vulnerabilities contributed to a growth in demand for IT professionals that outstripped the growth of industry in general. This “skills boom” and the commensurate pay increase is helping drive home an important lesson for operators in every industry: Cyber security is no longer something we can take for granted.
From the storage of critical resources in the cloud to server-based data collection programs, a string of recent and high-profile breaches has left companies and their IT teams wondering: What can we do to keep ourselves protected in 2018?

Depending on your level of expertise, it might surprise you how inherently vulnerable traditional email is in the year 2017 — and will remain in 2018. In fact, good email hygiene should be a cornerstone of any formal employee training program you devise with cyber security as its mission.
What is good email hygiene? It means discarding — without opening — any suspicious email you receive from an unknown sender. You should also take advantage of any options your provider makes available concerning “remote content.” It’s usually possible to set your email client to not automatically download images and other in-message assets that are stored on a remote server. Finding this option in your settings menu can shut down one more potential vector of phishing attacks.
Unfortunately, today’s would-be hackers have even more sophisticated tools at their disposal than these. It’s possible you’ll receive — or have already received — an email that looks like it was sent by somebody in your address book. Your clue might be strange phrasing, a tone you’re not familiar with or a request to clink a questionable link. If you get an email like this, discard it immediately and let the party in question know what happened. One of their accounts may have been compromised.
This has been go-to advice for the security-conscious for years, but people still get it wrong, so it bears repeating. Modern software is — or should be — updated regularly for a very important purpose. Not every new feature or line of code is immediately apparent to the user, but developers might release critical updates to plug serious vulnerabilities behind the scenes.
Remember Wannacry? By the time the average user became aware of the type and scope of the problem, most major hardware and software providers had already adapted their code to account for the new vulnerability and already pushed the fix to users’ devices.
Here’s the kicker: if you’d had automatic software updates turned on, or had even performed one manually when prompted, you’d never have even needed to be aware there was a problem. Bliss in ignorance? Perhaps — but it underscores just how efficient technology companies have become at answering new hacking attempts in kind. Wannacry was spread predominantly by out-of-date copies of Windows that their owners had neglected to update.
So? If you haven’t already, take a look at when and how your personal and work computers and devices perform updates. Leaving your machines on overnight isn’t exactly “green,” but it can make the installation of critical software updates painless to the point where they don’t interrupt your workflow during the day.

First, the good news: By and large, cloud storage is safer than we tend to give it credit for. And that’s a good thing, because a lot of us rely on the cloud for our livelihoods.
And really, isn’t the ability to immediately retrieve important files, in itself, a kind of cyber security? Beyond the obvious convenience factor, this represents knowledge that if the worst should come to pass — from a natural disaster to a sickly hard drive platter — your most important assets are stored safely and redundantly.
It’s a natural feeling to think of cloud storage as this precarious arrangement where your data is “out there” and ripe for the plucking — but this popular mentality isn’t quite accurate. The cloud storage providers who’ve earned their positive reputations store your data in physically secure data centers that are generally well-insulated against hacking attempts.
There are two important caveats about this, though:
1. It’s important to remember that cloud storage is a two-way street. If a file on your desktop computer is infected with malware or a virus and it’s uploaded onto your cloud server, the “cloud version” of that same file will be overwritten with the compromised one. Take some time to study your workflow for details like this and ensure your local machine is protected satisfactorily. More on that in a moment.
2. The weaker aspects of cloud storage protection — your username and password, mostly — are still only as safe as you make them. Use strong passwords every time and seriously consider a password generator and organizer like 1Password or LastPass, depending on your platform of choice.
Modern business happens just about anywhere — that’s part of the charm of cloud storage in the first place. You don’t want to miss out on the ability to expand the reach of your business or perform important tasks in the field, so don’t eschew this technology simply because of security worries. With the right partner and the right attention to details, your data should be, as the saying goes, safe as houses.

We get so caught up in worrying over the length of our passwords that we sometimes forget the more physical dangers associated with cyber security: vulnerable devices.
As cloud storage helped us take our business lives mobile, logic boards shrunk in size to make sure computers were there waiting for us. Now, many of us perform a considerable number of our work-related tasks on company-owned and even personal smartphones, tablets, netbooks and laptops. As you can probably imagine, this is a bit of a cyber security can of worms.
Set each of your devices to automatically lock the screen after a reasonable interval. It’s good for battery life, and it’s good protection against prying eyes.
Next, make sure you only install software from known providers. Both of the major mobile app stores are infamous for letting sneakily designed or deceptively named apps through their screening process, some of which users may install believing they’re the “real deal.”
Also, since our digital lives tend to occupy several apps and software platforms, move through your devices app by app and lock down everything of a sensitive nature. Most operating systems make it easy for third-party developers to leverage physical security measures like fingerprint readers and now Face ID in their own code.
Translation? Enabling tighter security measures in each app adds additional peace of mind for those occasions when you forget to lock your screen or you leave your device unattended. Can you really be too protected?
Anyone who’s honest will tell you they’ll exhaust their allotted word count before they run out of cybersecurity tips for 2018. It’s true that there’s always something new to learn, but it’s also true that technology becomes paradoxically safer even as it grows more vulnerable. Suffice it to say, the good guys work just as hard to keep us safe as the bad guys do to threaten our data.
As a final note on where our digital tools might take us in the future, be mindful also of the emerging bring-your-device culture in the modern office. This is a terrific employee perk, but as a team leader or IT specialist, it’s up to you to make sure you have training and protocols in place to educate your employees on good security practices and to standardize how they protect your company’s valuable information.
If anything, that’s the takeaway here: there’s strength in our collective understanding of cyber security best practices. Hopefully this has given you some good places to start.
We’ve all heard the nightmare stories about businesses whose websites have been hacked and taken down. Read our recent article/checklist to see how healthy your website is. Click here.

Lexie Lu is a contributing writer for Splendor Design and a freelance designer. She enjoys writing code and learning about new web platforms. She manages Design Roast and can be followed on Twitter @lexieludesigner.

What’s better than continuously being recognized for outstanding CRE branding and marketing? Not much, really.
read more
While many companies invest in advanced technology, true success comes from harnessing the power of human intelligence and creativity.
read more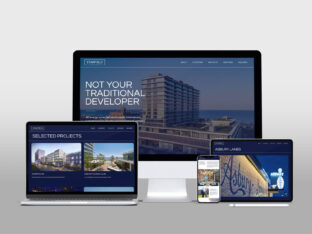
With a new name and identity in hand, Starfield Companies looked to Splendor for a website design that reflects the company values.
read more